

An abattoir also needs access control and time and attendance systems controlled by biometrics technology that is able to tell a hoof from a thumb.
Vencor Holdings, an abattoir located in Polokwane, required a solution to better control its access, mainly for security and health reasons. The company, which employs dozens of workers, needed a solution to better control access to the building and also to restrict certain areas to employees.
The abattoir; which had no previous access solution installed, thought long and hard about what type of access solution it would use. It had to be one that was robust, simple to use and manage, and overall something that was quick to install – thereby keeping disruptions to the day-to-day operations of the business to a minimum.
After careful consideration and by recommendations by its clients, Vencor Holdings opted for Sagem MA 500, 200 and 100 fingerprint readers and Turnstar turnstiles for access control.
Vencor’s focus when implementing this solution was to address the issues of security and health. A company spokesperson said that Vencor Holdings mainly deals with two types of employees: those involved with slaughtering the animals and those working with the meat once it has been removed from the animal. “It is absolutely imperative that these two groups of employees be confined to their associated working areas, should an employee move from his or her designated work area to the other, meat could be contaminated, costing us thousands.”
By installing fingerprint readers along with turnstiles supplied by CI Polokwane, Vencor Holdings was able to implement a solution that not only improved security but also enforced the strict health laws abattoirs have to adhere to. According to Vencor Holdings, absolutely no convincing was needed, the company knew what it needed to do and it experienced absolutely no obstacles when having the installation installed.
Added HR benefits
Once the solution was implemented and operational, Vencor Holdings found that the tight integration of this solution with its existing payroll package meant that it could more closely monitor the work times of its employees. Once the solution was installed, each employee had to scan his or her finger in order to gain access. This had a positive pay off as the company is now also able to monitor staff’s working hours much closer than before.
Although the solution implemented by CI Polokwane at Vencor Holdings was rather small, it is effective. The solution comprised a total of two turnstiles and three gates. The gates and turnstiles along with the necessary software in order to operate them was installed in one week. The turnstiles, gates and fingerprints were installed over the weekend, software was loaded onto the various machines on the Monday and Tuesday and the finger enrolment took the rest of the week.
When asked what Vencor Holdings would do differently, the company merely stated that it was satisfied with the solution and would recommend that companies looking for a similar solution look for a completely integrated one.
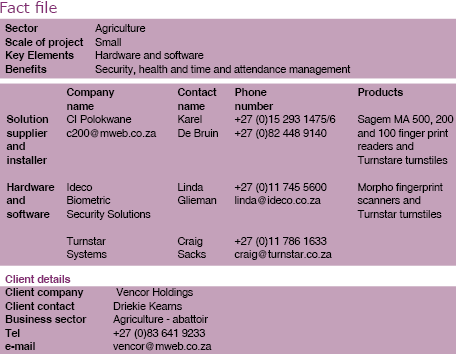
For more information contact Karel de Bruin, CI Polokwane, +27 (0)15 293 1475/6, [email protected]
© Technews Publishing (Pty) Ltd. | All Rights Reserved.