
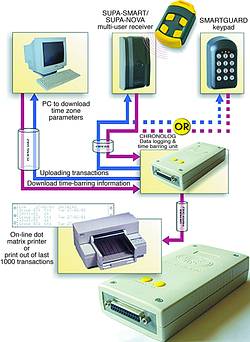
The ChronoLog, an access control solution from Centurion Systems, offers both the ability to record access transactions, and control access on a time basis.
Since its inception, the ChronoLog has had the ability to link to Centurion's range of townhouse-based receivers (SupaNova and SupaSmart). Linking the ChronoLog to a receiver allows an accurate record of the last 1000 transmitter transactions to be stored in memory. This information can be retrieved and queried in the event of an incident occurring. Additionally, the ChronoLog gives the supervisor the ability to limit transmitter access to certain times of the day.
These access control features are not just limited to the townhouse-based receivers. Centurion's Smartguard keypad has recently been upgraded to offer ChronoLog interface capabilities. This allows an unprecedented level of access control on a keypad based access system. Every keypad access-transaction is logged and valid access is only granted based on the time parameters that are associated with the access code.
In an effort to meet the practical demands of an access control installation, Centurion Systems has developed a line extender (CL/DAXKIT1). In the past, the ChronoLog has had to be placed close to the programming console of the townhouse receiver, or now the keypad. This is not always convenient from an installation perspective particularly with the keypad. With the new line extender interface, the ChronoLog can be positioned up to 30 m away from the access head (townhouse receiver or keypad).
These features are offered at an affordable price relative to the conventional access control systems on the market.
For more information contact Centurion Systems, 011 699 2400.
© Technews Publishing (Pty) Ltd. | All Rights Reserved.