
The first place in the quarterly chart for South Africa is taken by Trojan.AutorunInf.Gen, with a percentage of 14,49. This Trojan is constantly amongst the most 'popular' e-threats as it easily spreads via removable devices and Windows shared folders. The Windows Autorun is intensively exploited by malware authors to force the execution of dangerous files located on infected USB drives.
Malware top for July - September 2010:
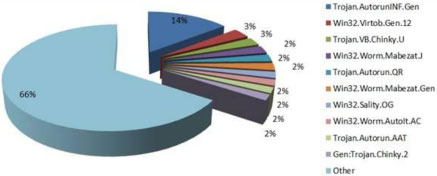
Occupying the second place, with 3,08% of the total amount of malware in South Africa, Win32.Virtob.Gen.12 is a newcomer with great 'negative' potential. This virus infects files, blocks access to security websites and it may also inject an iframe in web files such as .HTM, .PHP or .ASP.
Ranking third and accounting for 2,50% of the malware detections in South Africa, Trojan.VB.Chinky.U has a worm component which allows it to spread using flash drives and other media, such as USB external hard disks and even mapped drives across the network. Furthermore, the downloader component of Trojan.VB.Chinky.U would subsequently drop and install other e-threats on the infected system, such as backdoors, password stealers, rogue AV and other offers that are too hot to handle.
Ranking fourth, with a percentage of 2,39, there is Win32.Worm.Mabezat.J. This worm spreads via e-mail attachments and, most of the times, it is camouflaged as a perfectly innocent Word document amongst others, advertising various jobs. What is particularly important about Win32.Worm.Mabezat.J is that it is also able to infect executables by replacing the first 1768 bytes of such files with its own encrypted body.
The fifth place goes to Trojan.Autorun.QR, an encrypted autorun file that is widely used to automatically launch specific worms located on infected flash drives as soon as they are plugged into a computer with the Autorun feature enabled. Among those that make use of this Trojan there is this quarterly top’s fourth contender Win32.Worm.Mabezat.J.
The BitDefender July – September 2010 Top 10 E-Threat list in South Africa includes:
1. Trojan.AutorunINF.Gen 14,49%
2. Win32.Virtob.Gen.12 3,08%
3. Trojan.VB.Chinky.U 2,50%
4. Win32.Worm.Mabezat.J 2,39%
5.Trojan.Autorun.QR 2,24%
6. Win32.Worm.Mabezat.Gen 2,21%
7. Win32.Sality.OG 1,89%
8. Win32.Worm.AutoIt.AC 1,81%
9. Trojan.Autorun.AAT 1,74%
10. Gen:Trojan.Chinky.2 1,74%
Other 65,90%
For more information contact Alina Anton, Senior PR and marketing coordinator, EMEA & APAC Business Unit, BitDefender, +40 212 063 470, www.bitdefender.com , [email protected]
© Technews Publishing (Pty) Ltd. | All Rights Reserved.