
Fingerprint biometrics has been around for a relatively long time now and some companies have even been involved in its development for more than 25 years.
It is still, however, a subject that, relatively speaking, very little is known about in terms of how it works and why it is far superior in its technology and practicality than other forms of biometric identification. So how does fingerprint biometrics work and what makes certain fingerprint readers superior to others?
Below are the answers to some of those questions from the biometric technology experts within the ACE group:
What are minutia points?
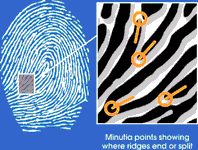
The pattern of a fingerprint is made up of ridges and valleys. Minutia points occur where ridges split or end and their precise location is represented by the symbol on the left.
How are minutia points used in fingerprint technology?
On average, a fingerprint has 85 minutia points, creating a unique pattern or template that distinguishes one fingerprint from all others. During enrolment, scanning technology converts and stores this unique template as a mathematical code. Identification is achieved when a scanned fingerprint is matched to its stored template.
Why is fingerprint biometrics better than other forms of biometrics?
Fingerprints are recognised world-wide as the forensic norm for biometric identification and are easily lifted from a crime scene and used for identification in criminal investigations. Fingerprint readers are easy to use and to understand and can be used without fault in a wide variety of applications and operating environments as opposed to other forms of biometrics.
Dirty and damaged fingerprints cause inferior fingerprint technologies to register false minutia points, and as a result do not function in harsh operating environments. Severely damaged or dirty fingerprints often introduce up to 50 false minutia points. If the biometric algorithms being used are unable to distinguish this false information from true information, false rejections and even worse, false acceptances become increasingly probable. Some biometric companies have developed sophisticated algorithms which are able to successfully and consistently detect and reject these false minutiae.

© Technews Publishing (Pty) Ltd. | All Rights Reserved.