
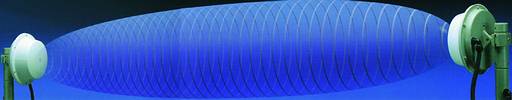
Microwave detection in security applications has been around for over 20 years as an extremely effective form of motion detection. Its main advantage is that it is able to detect over large areas and it is also able to detect through glass, walls, dry walls and partitioning.
With the advent of digital technology over the past 10 to 15 years, microwave detection products have developed and improved in leaps and bounds and with the inclusion of 'fuzzy logic' into microwave detection, which allows the manufacturer to pre-program the detectors with simulations events that could constitute an alarm. For example the movement patterns of a human intruder or a vehicle is programmed into the detector, enabling the microwave detector to make decisions on size of targets, speed of target, duration of target in zone, in other words, the detector has a basic artificial intelligence.

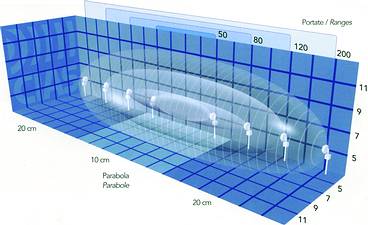
Microwave is not just a point-to-point detection it is also a volumetric detection device.
New alignment tools and software have also been developed to assist the installer with the installation, calibration and setting up these detectors with pinpoint accuracy.

Over the last five years microwave detection has developed to also include online network capabilities and has become the preferred perimeter detection device for high security applications and is popular in the South African market especially in the gold, platinum and diamond mining, petroleum and gas industries as well as electrical sub stations, telephone exchanges and cellphone repeater stations. Internationally, this technology has been introduced into other industries such as the military, air force, navy and airports.

SEC (Security Equipment Centre) distributes the range of CIAS microwave detection solutions and also manufactures, imports and distributes a full range of electronic security products through a national distribution network. SEC offers a comprehensive range of perimeter detection, access control systems, electric and magnetic locks, alarm systems, random selectors, door interlocks and power supplies.
For more information contact Domenique Testa or Gordon Prentice, SEC, 011 452 1410, [email protected]
| Tel: | +27 11 452 1410 |
| Email: | [email protected] |
| www: | www.secsa.co.za |
| Articles: | More information and articles about Security Equipment Centre |

© Technews Publishing (Pty) Ltd. | All Rights Reserved.