
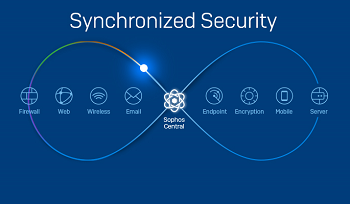
Synchronised Security is a complete portfolio of security products that work together to automatically respond to threats. The portfolio is managed through a single web-based console. It reduces your cyber risk, increases cross-estate visibility and greatly improves your security ROI (return on investment).
This complete security portfolio from Sophos offers endpoint, servers, firewall, Wi-Fi, mobile, email and encryption that is fully scalable to grow as your business does. You can start with one product and add more as you need them.
These cybersecurity products actively work together, they automatically respond to incidents and deliver enhanced security insights. There are no additional subscriptions required so deployment is easy.
Reduce cyber risk
Zero-touch incident response slashes exposure to threats while the integrated product portfolio minimises security gaps. Enhanced insight into network traffic lets you identify and address hidden risks. Centralised management enables you to focus on priority alerts.
You can link malicious traffic to specific devices or users, this allows you to isolate infected endpoints to block further lateral movement within the network.
Enhance cross-estate visibility
Seeing all your cybersecurity in one place, with one source of truth, enables you to see what’s going on in real-time, while the ability to correlate traffic to users and computers extends your insight and enables you to address issues.
Synchronised Security delivers unmatched visibility by sharing and correlating real-time information. It identifies all network traffic – if the XG Firewall sees an application that doesn’t match a known signature, Sophos Intercept X and Sophos Intercept X for Servers provides the application name, patch, and category in seconds. This solution can also link traffic to individual computers and users.
Increase return on investment
This solution enables you to deliver superior benefits from your security resources. Automated incident response frees up IT teams, while centralised management slashes day-to-day overheads. With a Security Heartbeat, Sophos products share real-time information and then respond automatically, in seconds. This zero-touch incident response slashes your exposure to threats while freeing up IT resources.
According to Ross Anderson, Sophos product development manager at Duxbury Networking, “83% of IT managers say malware threats are harder to stop now compared to last year. Why? Because cybercriminals connect multiple techniques into their advanced attacks while most security products still work in isolation. In contrast, with Synchronised Security, Sophos products work together as a coordinated system, advancing your threat protection while also reducing your costs.”
This advanced technology from Sophos streamlines cybersecurity management to save you and your business time, cost, and effort every day. You can manage everything through the intuitive Sophos Central platform, it allows you to view and control your cybersecurity on a single console. The common interface for all products always delivers consistency and usability. Sophos Central is cloud-based, so you can access it at any time and from any location while eliminating server overhead costs.
By automating incident response, delivering new security insights, and simplifying management, Synchronised Security reduces risk, enhances cross-estate visibility, and allows organisations to scale their security without scaling their resources.
© Technews Publishing (Pty) Ltd. | All Rights Reserved.