
The Covid-19 pandemic and the shift to work-from-anywhere has forced organisations to significantly advance their digital acceleration initiatives, resulting in increasingly hybrid IT networks to help deliver better access to applications and data. In many cases, these assets are distributed across data centre networks and cloud deployments that are in a constant state of flux.

In addition to the added complexity of managing hybrid IT architectures, organisations underwent forced acceleration to the cloud due to external factors such as competitive pressures or supply chain issues. The lack of time to properly plan and coordinate around these efforts has led to security gaps across an expanded attack surface. Now, today’s organisations are scrambling to provide consistent security and policy everywhere to defend against attacks without disrupting business operations.
So given this digital acceleration, what is the current state of cloud adoption and cloud security? Fortinet partnered with Cybersecurity Insiders to survey more than 800 cybersecurity professionals from around the world and across industries. The 2022 Cloud Security Report reveals how security executives and practitioners are using the cloud, how their organisations are responding to security threats in the cloud, and the challenges they are facing. Some of the highlights from this year’s report follow.
Digital innovation accelerates cloud adoption
Organisations continue to shift workloads to the cloud at a rapid pace to achieve faster time to market, increased responsiveness to customer needs and cost reductions. 39% of respondents have more than half of their workloads in the cloud.
Most organisations are selecting either a hybrid-cloud (39%, up from 36% last year) or multi-cloud deployment approach (33%) to integrate multiple services, provide scalability or ensure business continuity. 67% of organisations currently use two or more cloud providers. AWS and Microsoft Azure currently top the list, though Google and Oracle are rapidly increasing their investment and market share.
Cloud adoption faces headwinds
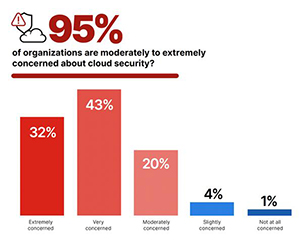
This year’s Cloud Security Report is set against a backdrop of increasingly brazen and costly ransomware attacks, and the major disclosure of a severe zero-day vulnerability in the popular Apache Log4j logging tool, used in many enterprise apps and cloud platforms. It’s not surprising that 95% of organisations are moderately to extremely concerned about cloud security.
When Cybersecurity Insiders asked what surprises security professionals uncovered that hinder cloud adoption, they discovered lack of visibility, high cost, lack of control and lack of security are the biggest unforeseen factors that slow or stop cloud adoption. These remain consistently the top inhibitors of cloud adoption when comparing against previous surveys. Addressing these topics is critical to empowering business success.
The survey also reveals that the biggest challenges organisations face are not primarily about technology, but people and processes. Lack of qualified staff (40%, up from 37% last year) is the biggest obstacle to faster adoption, followed by legal and regulatory compliance, and data security issues. Internal upskilling as well as external expertise are major game-changers to accelerating cloud success.
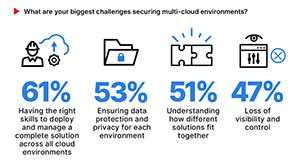
And with most organisations choosing a hybrid or multi-cloud strategy, not surprisingly, they face increased complexity and security challenges. Lack of security skills becomes the top challenge (61%, up from 57% last year), followed by data protection, understanding how different solutions fit together, and loss of visibility and control. Simplifying this complexity is key.
Breaking down the barriers to cloud adoption
To reduce complexity and increase security effectiveness, visionary organisations are taking advantage of a cybersecurity mesh platform. This collaborative approach helps to dramatically reduce the financial impact of security incidents. With threat intelligence shared directly across diverse attack vectors, visibility, management and automation are simpler, meaning that threats are identified and mitigated faster. Ultimately, this reduces complexities, resolves cloud cybersecurity skills and resource gaps, and increases overall security effectiveness.
It’s no surprise that over three-quarters (78%) of respondents consider it very or extremely helpful to have a single cloud security platform to protect data consistently and comprehensively across their cloud footprint.

© Technews Publishing (Pty) Ltd. | All Rights Reserved.